Twilight Tech LLC — Managed IT and Cybersecurity Services Atlanta Georgia
Enterprise-grade IT support and cybersecurity — delivered with clarity, consistency, and a security-first mindset at a price point that makes sense for the businesses that can't afford to be breached.
Choose Your Protection Level
Subscription-based IT support with cybersecurity baked in — flat monthly pricing, no surprises, no lock-in tricks.
- Remote help desk support (business hours)
- Microsoft 365 user & account support
- Password resets & account lockouts
- Endpoint health & uptime monitoring
- OS & application patch management
- Microsoft Defender antivirus
- Monthly system health summary
- Everything in Essentials, plus:
- Identity & Access Management (Entra ID)
- MFA enforcement & conditional access
- Email security & phishing protection
- Automated backup monitoring & restores
- Patch compliance reporting
- Security baseline hardening
- Quarterly security review
- Everything in Secure, plus:
- Endpoint Detection & Response (EDR)
- Huntress threat hunting & managed detection
- Vulnerability scanning & remediation
- Security event monitoring (SOC-lite)
- After-hours emergency support
- Monthly executive security report
- Incident response support
Full Plan Comparison
| Feature | Essentials $75/user |
Secure ⭐ $125/user |
Sentinel $175/user |
|---|---|---|---|
| Remote Helpdesk Support | ✓ | ✓ | ✓ |
| Microsoft 365 Support | ✓ | ✓ | ✓ |
| Endpoint Monitoring | ✓ | ✓ | ✓ |
| Patch Management | ✓ | ✓ | ✓ |
| Microsoft Defender AV | ✓ | ✓ | ✓ |
| MFA Enforcement | — | ✓ | ✓ |
| Identity & Access (Entra ID) | — | ✓ | ✓ |
| Email Security & Phishing Protection | — | ✓ | ✓ |
| Backup & Verified Restores | — | ✓ | ✓ |
| Quarterly Security Review | — | ✓ | ✓ |
| Advanced EDR (Huntress) | — | — | ✓ |
| Vulnerability Scanning | — | — | ✓ |
| After-Hours Emergency Support | — | — | ✓ |
| Monthly Executive Security Report | — | — | ✓ |
| SLA Response Time | Same business day | 4 hours (biz hours) | 1 hour emergency |
How Support Works
We audit your users, devices, and M365 environment to understand your current security posture and identify gaps.
RMM agents, endpoint protection, and backup tools are deployed across all devices with zero disruption to your workflow.
MFA enforced, admin accounts secured, security policies applied. Your environment is hardened to Twilight Tech standards.
Everything is documented — credentials, network diagrams, SOPs, vendor contacts. Nothing lives only in someone's head.
Orientation call, support walkthrough, and your dedicated support channel goes live. You're officially Twilight Tech managed.
Browse the À La Carte section. Not sure? Book a $50 IT Consultation and we'll tell you exactly what you need — the fee gets credited to any service you book.
Use the intake form below, or email support@twilighttech.io. Describe your situation and we'll confirm same day.
You'll receive a flat-rate invoice before any work begins. Pay once, no surprises. Work starts after payment is confirmed.
Most services are completed remotely within 24–48 hours. You'll get a full summary of everything done.
That's it. You're not subscribed to anything. Managed plans are here when you're ready — but there's zero pressure.
🛡️ Twilight Sentinel — AI Security Platform
Our next-generation Sentinel platform uses AI-assisted cybersecurity analysis to continuously scan your domain, analyze security risks, and generate actionable threat reports. Coming soon for managed clients.
Join the Early Access ListNo Subscription Required
Not ready for a managed plan? No pressure. Every service below is one-time, flat-rate, and zero commitment.
- Current environment review
- Prioritized recommendations delivered
- $50 credited toward any service you book after
- Written summary follow-up included
- Domain & email breach scan
- Exposed credential identification
- Breach source & date documented
- Branded report with action steps
- Full malware & adware removal
- Startup optimization
- Disk cleanup & storage recovery
- Driver & OS updates applied
- Performance verified before & after
- User account + licensing + MFA
- Laptop OS, Entra enrollment, Defender
- Required software installed
- Ready before their start date
- Dark Web Scan + branded report
- MFA enabled for all users
- Conditional access policies applied
- Admin accounts secured + hardened
- New Business IT foundation
- Microsoft 365 tenant fully configured
- MFA + security baseline applied
- Cloud backup configured + tested
- Account disabled + access revoked
- Data secured + retention configured
- Licenses recovered + documented
- Audit trail for compliance
- Account creation + licensing
- MFA setup + verified
- Group + mailbox access configured
- Documented + ready before start date
- OS configuration & updates applied
- Entra ID / domain enrollment
- Required software installed
- Defender & backup agent deployed
- MFA enabled for all users
- Conditional access policies applied
- Admin accounts secured
- Security baseline hardening
- M365 mail, OneDrive, SharePoint backup
- Endpoint backup for laptops/desktops
- Daily backups + 30-day retention
- Recovery tested before handoff
- Domain & email routing configured
- Users set up & properly licensed
- MFA enforced for all accounts
- SharePoint & OneDrive configured
- Admin account secured & documented
- MFA + access audit
- Vulnerability scan
- Written report w/ prioritized remediation
- Year-over-year tracking when repeated
- Microsoft 365 configured & secured
- Business email on your domain
- MFA enforced from day one
- Security baseline applied
- Backup solution set up & tested
- Available to non-managed clients
- Malware, ransomware, breach response
- Containment & recovery
- Post-incident documentation
- Overage at $99/hr quoted post-block
- Mail, calendar, contacts migrated
- Drive content migrated to OneDrive
- Domain + MFA configured
- Mailboxes 6+ quoted via consultation
- HIPAA policy templates delivered
- MFA enforcement + access policies
- Audit log baseline configured
- 1-hour live Q&A session
- PCI policy templates delivered
- MFA enforcement + access policies
- Network segmentation review
- Scan baseline + 1hr live Q&A
- Twilight Essentials — $75/user/mo
- Twilight Secure — $125/user/mo (⭐ recommended)
- Twilight Sentinel — $175/user/mo (full SOC-lite)
- No contract · cancel anytime
We Build AI That Works For You
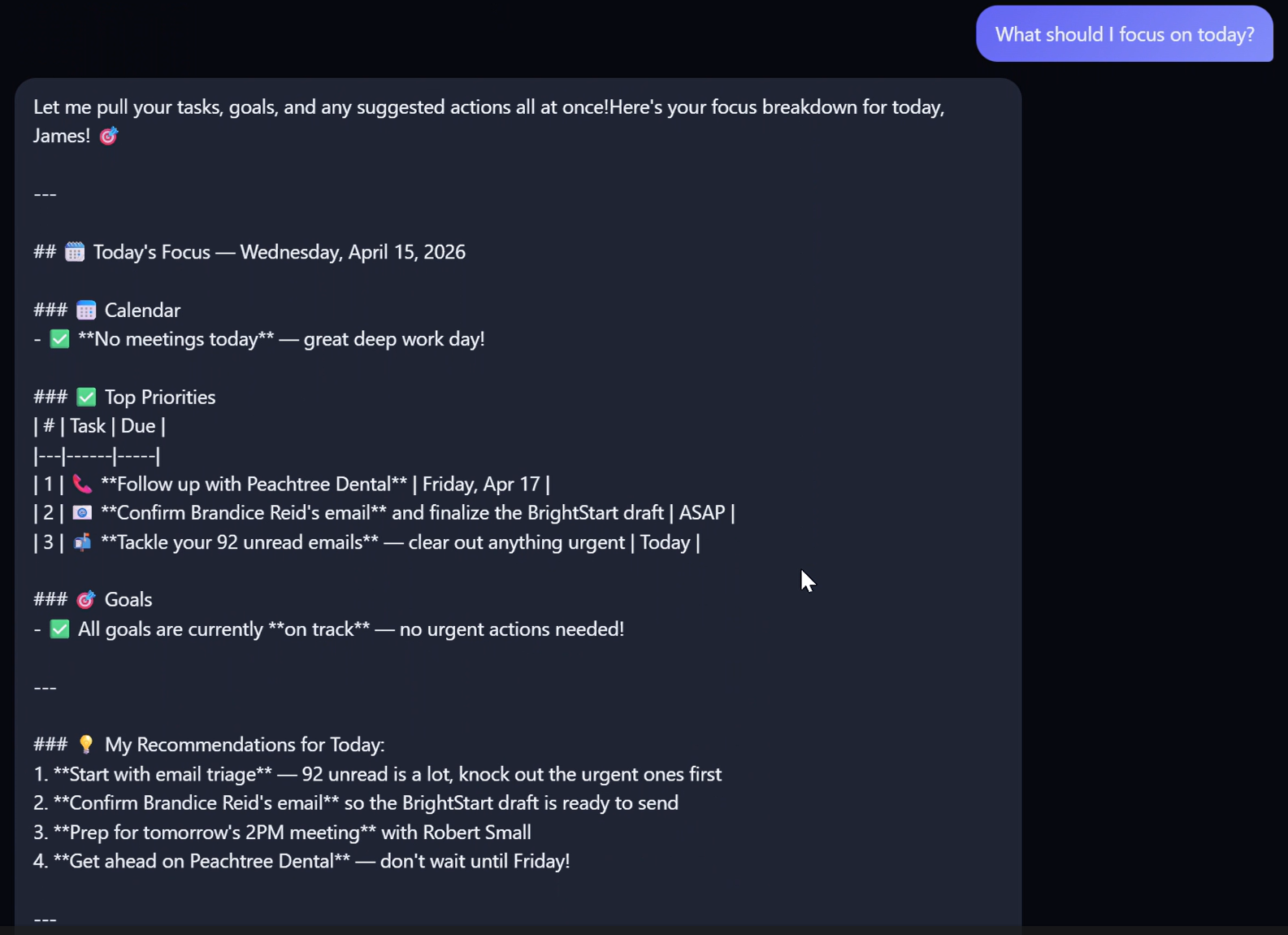
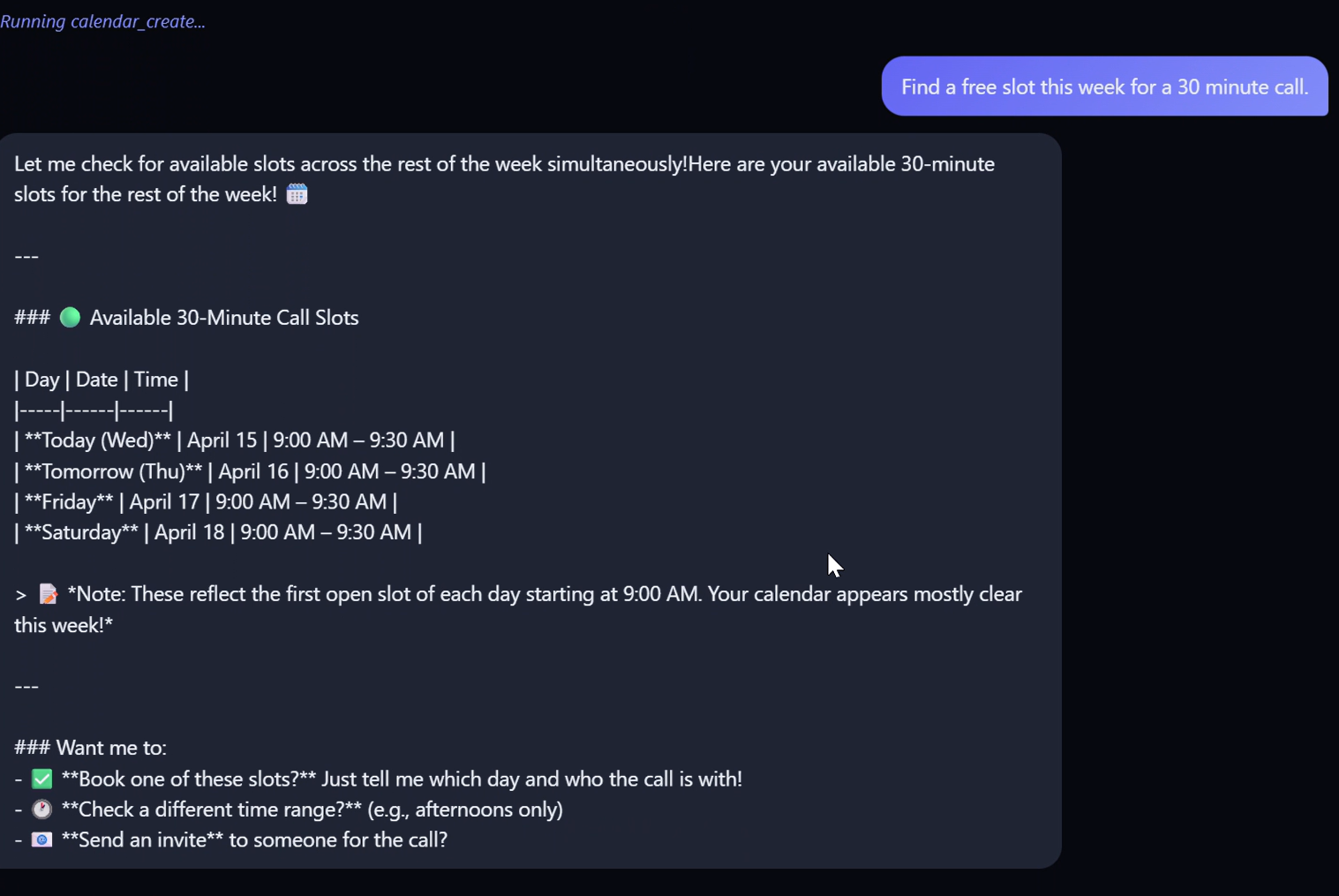
Custom AI assistants that manage your operations, automate your workflows, and run your business — hands-free. Not a pitch deck. A deployed system.
We don't just talk about AI — we build it, deploy it, and prove it works. Our AI systems manage emails, schedule meetings, monitor security, track projects, and handle client operations — all from a single natural-language command.
What We Build
AI Assistants
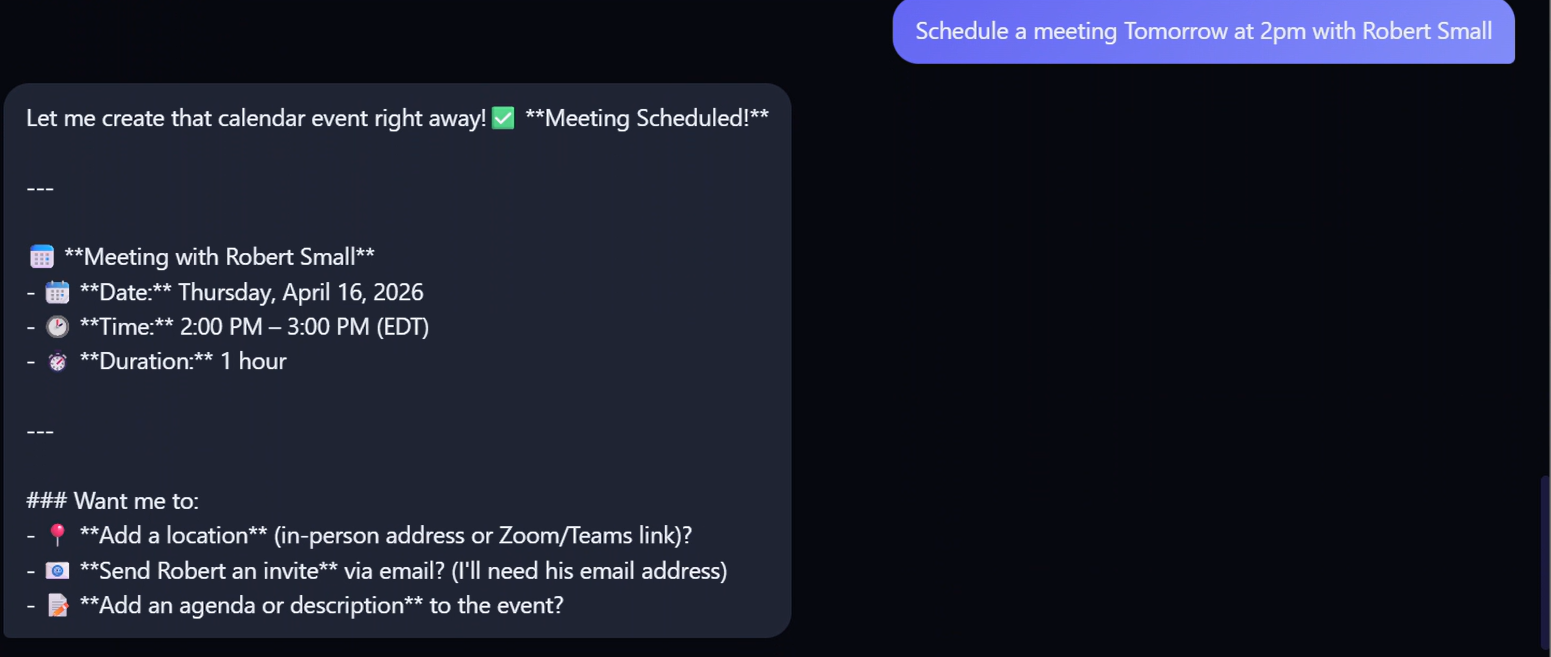
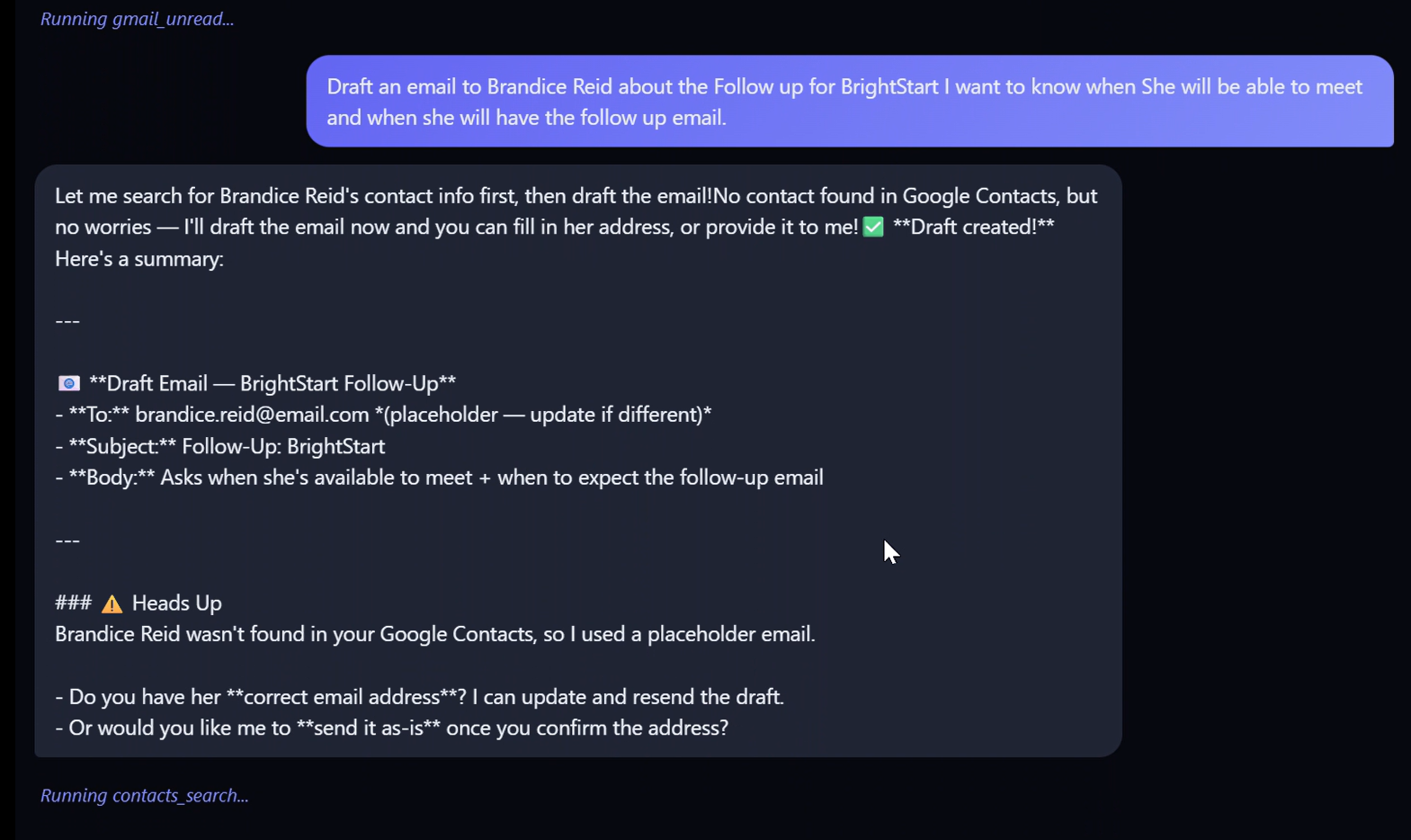
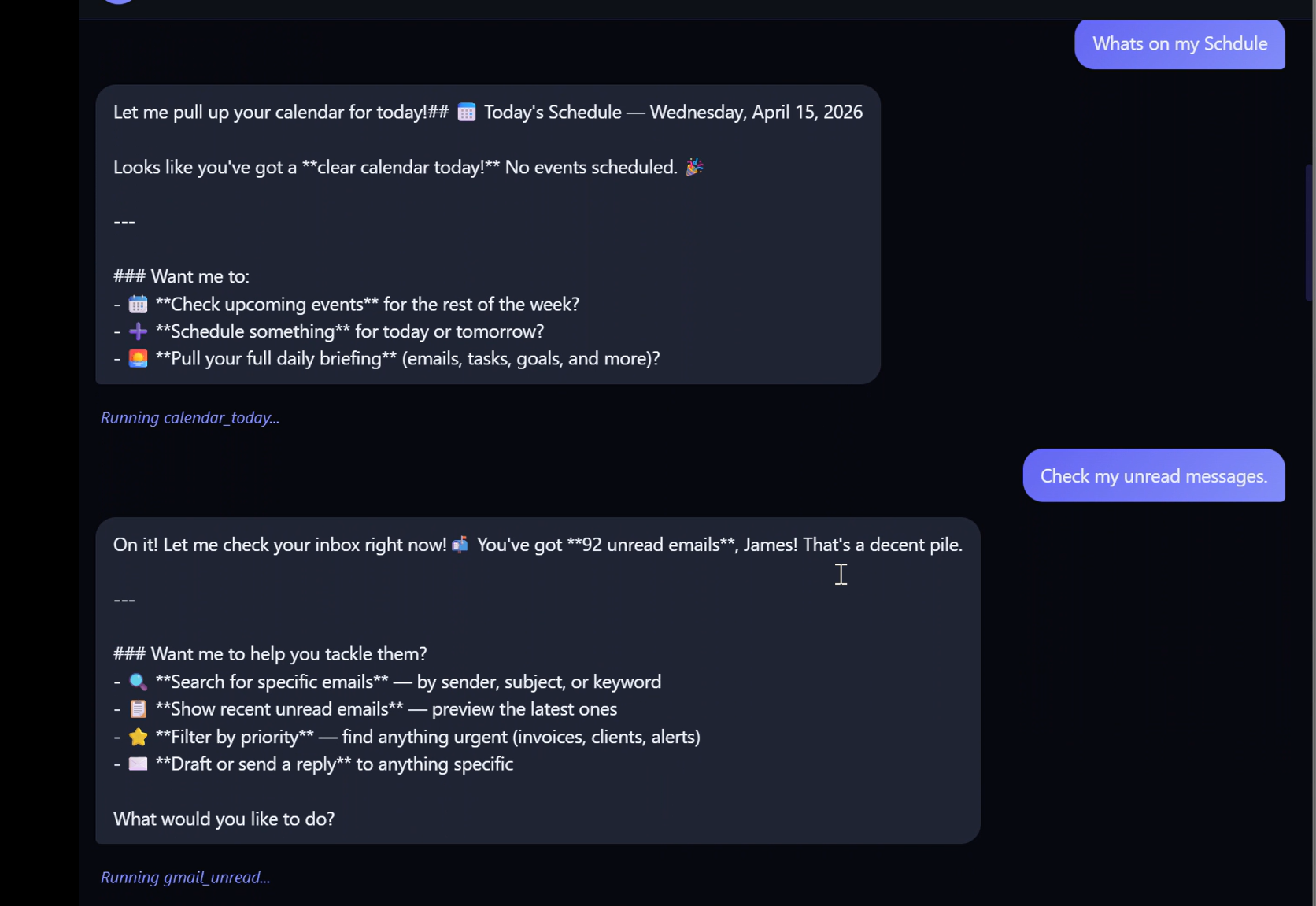
Custom AI that understands your business — manages emails, schedules meetings, answers questions, and handles operations through natural conversation.
Email & Calendar Automation
Send emails, find free slots, create events, and manage your inbox — all by telling the AI what you need in plain English.
Security Monitoring
Real-time system awareness — process monitoring, service health checks, USB detection, event log analysis, and proactive security alerts.
Business Dashboards
Live dashboards showing your KPIs, client pipeline, revenue, SLA compliance, and ticket status — updated in real time.
Telegram & Mobile Control
Control your AI assistant from anywhere via Telegram. Send commands from your phone and get instant responses.
Google Workspace Integration
Deep integration with Gmail, Google Calendar, Drive, Tasks, and Contacts. Your AI manages your entire workspace.
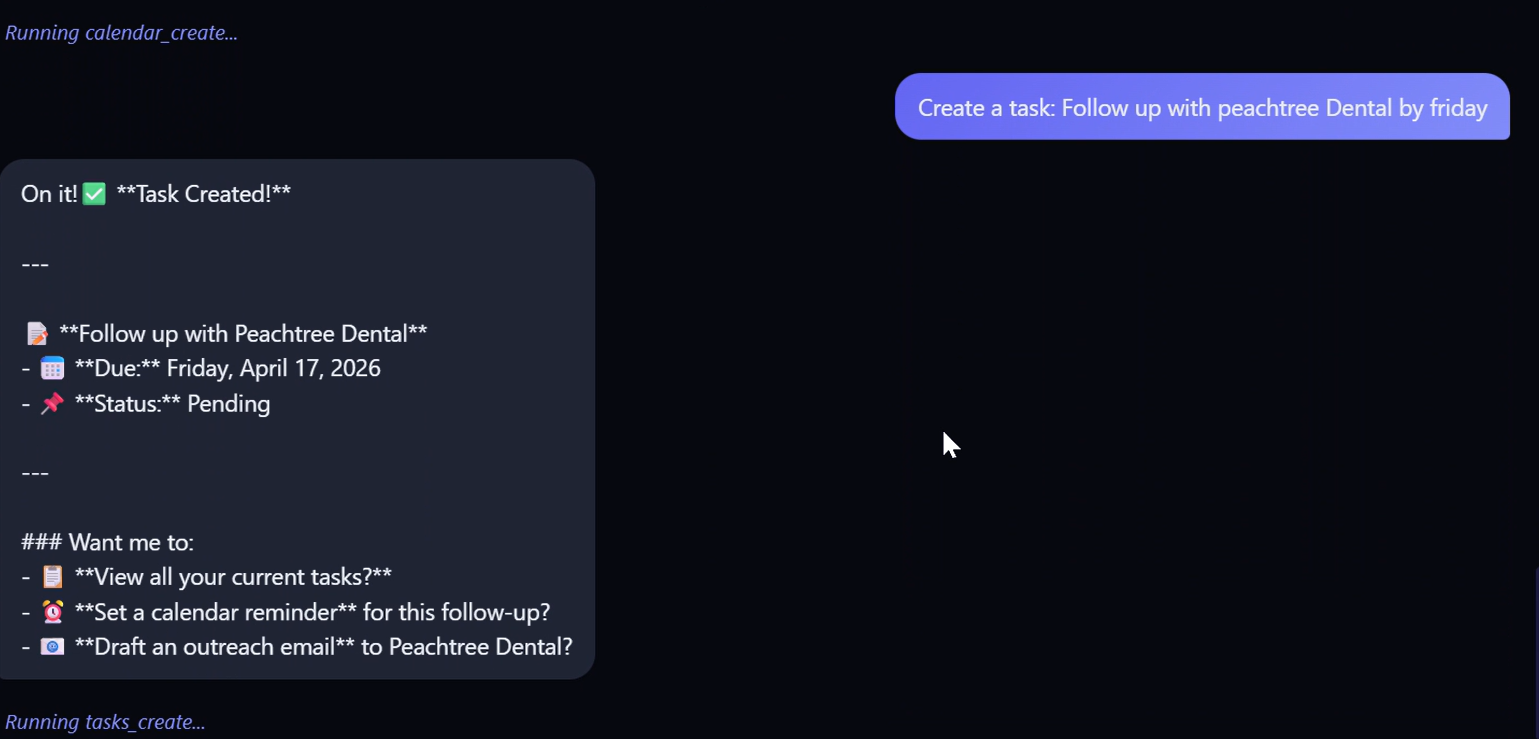
Project & Task Management
Track projects, milestones, blockers, and deadlines. AI-powered task creation, prioritization, and progress reporting.
Client Operations (MSP)
For managed service providers: automated ticketing, SLA tracking, client portals, outreach campaigns, and revenue reporting.
Your Network Has a Sentinel Now
A deployable security entity that watches traffic across your network, learns what normal looks like, and flags the stuff that doesn't fit — before you even get the call.
HackBot started as a purple-team toolkit. It's now a deployable security sentinel — a Docker-packaged server that plugs into your environment, learns what's normal for your network, and responds with judgment. Alerts land where your SOC already lives. Containment actions wait for your approval. Threat forecasts tell you what's coming, not just what already happened.
What HackBot Does For You
Learns Your Network
HackBot spends its first week learning what "normal" looks like in your environment. Per-client behavioral profiles across traffic, logins, processes, and data flows. When something actually changes, it notices.
Time-Aware Detection
A 3AM login is suspicious on Tuesday, normal for your 24/7 ops team. Baselines split across time-of-day and day-of-week so alerts fit the context of your business.
Tiered Autonomous Response
Some actions fire automatically. Some wait for your approval. Some require explicit triggers. One-click approve or deny. Kill switch halts everything.
Attack Forecasting
Not just "here's what happened." HackBot estimates breach risk per client, predicts CVE exploitation timelines, and tracks MITRE kill-chain progression so you see what's coming next.
Alerts Where You Live
Email, Slack, Telegram, PagerDuty, custom webhooks. Severity-adapted tone — critical alerts wake you up, low-priority waits for the daily digest.
Compliance, Built In
NIST 800-53, PCI-DSS, HIPAA, SOC 2. HackBot maps findings to framework controls so your auditors see gaps, not raw data.
Self-Healing
The watchdog has its own watchdog. HackBot monitors its own security services and self-heals before anything goes dark on your network.
Built on J-Bot
HackBot inherits the architecture that powers J-Bot — our flagship AI OS. Proven foundation, security-forged specialization.
How It Works
I Said It. It Did It.
Real commands. Real results. Every screenshot below is from a live, deployed system — not a mockup.
Watch the Demo
A real walkthrough of AI-powered operations — from natural language command to completed task.
Not Vaporware. Production Code.
Built & Deployed
- Not a pitch deck — a running system handling real operations every day
- 78+ tools across 5 specialized domains, all production-tested
- 3,800+ automated tests ensure nothing breaks when we ship
Security-First
- API key authentication, rate limiting, and audit trails on every action
- Real-time system monitoring — processes, services, event logs, USB devices
- Trust-gated operations — dangerous actions require explicit confirmation
Actually Intelligent
- Multi-provider AI with automatic failover — never goes down
- Learns your preferences, adapts to your workflow, remembers context
- Cross-domain reasoning — connects emails to calendar to tasks to projects
Access Anywhere
- Web dashboard, Telegram bot, or desktop companion — pick your interface
- Works from your phone, laptop, or server — wherever you are
- Real-time notifications when something needs your attention
Custom-Built
- Not a wrapper around ChatGPT — purpose-built AI with deep tool integration
- Every system tailored to your specific business needs and workflows
- White-label ready — your branding, your domain, your clients
ROI You Can Measure
- Track cost per AI operation — know exactly what you're spending
- Replace hours of manual work with seconds of AI automation
- Built-in budget controls so costs never surprise you
Ready to See What AI Can Do for Your Business?
Book a free 30-minute consultation. We'll show you a live system, not a slideshow.
Built by Someone Who's Done the Work.
Twilight Tech was founded by James "Twilight" Destrades Jr., an IT professional with over 8 years of hands-on help desk experience and a decade of customer service expertise. Based in Atlanta, Georgia, Twilight Tech brings enterprise-grade thinking to small businesses that deserve real protection.
This isn't a call center. Every ticket, every policy, every security configuration is handled with direct expertise in Microsoft environments, Active Directory, endpoint security, and identity management. Cybersecurity isn't an afterthought here — it's the foundation.
James has built and repaired custom PCs, deployed Microsoft 365 tenants, hardened endpoints, managed Active Directory, responded to security incidents, and built an AI-powered cybersecurity platform from scratch — 113,000+ lines of production code. Twilight Tech exists to make that expertise accessible to the businesses that need it most.
Experience Timeline
- Solo-designed and built a 113,557-line production platform combining agentic AI, multi-agent orchestration, RAG knowledge systems, and real-time LLM streaming
- Engineered a ReAct autonomous agent with 25 iterative reasoning cycles, 5-specialist multi-agent system, and deterministic scope enforcement
- Built multi-provider LLM abstraction (Claude, GPT-4o, Ollama) with automatic failover, token/cost tracking, and MCP server (21 tools)
- Architected event-driven enrichment pipeline with Redis pub/sub, connecting async scanning to AI threat analysis
- Shipped native desktop companion with voice I/O, trust-gated agent, and Tauri/Rust installer
- Administered Microsoft 365, Active Directory, and Azure AD environments supporting hundreds of users
- Provided Tier 1-2 support: account provisioning, Group Policy, hardware troubleshooting
- Managed endpoint deployment, imaging, and lifecycle across Windows environments
- Created SOPs and documentation that reduced average ticket resolution time
- Translated complex technical issues into clear guidance for non-technical stakeholders
- Developed client communication skills critical for MSP consulting and cybersecurity advisory
AI Engineering Competencies
Agentic AI Systems
- ReAct (Reason-Act-Observe) autonomous agent with 25 iterative reasoning cycles
- Claude API tool_use integration with 5 core tools and adaptive strategy engine
- 23 failure-pattern recognizers triggering automatic technique pivots
Multi-Agent Orchestration
- 5-specialist system (Recon, Vuln, Attack, Defense, Report) with task classifier routing
- Typed inter-agent communication via Pydantic models with semaphore concurrency
- Dependency-ordered execution with shared context propagation (1,500+ lines)
LLM Architecture
- Multi-provider abstraction (851 lines) — Claude, GPT-4o, Ollama + offline fallback
- Token/cost tracking with ContextVar injection, budget alerts, 11 REST endpoints
- 5-domain intent classifier with 40+ regex patterns and confidence scoring
RAG & Knowledge Systems
- Entity-relationship knowledge graph with Dijkstra-based attack chain pathfinding
- 3-tier memory system: working + episodic + knowledge base
- Cross-engagement episodic learning feeding back into agent reasoning loop
Real-Time AI Streaming
- WebSocket chat with async-generator streaming for token-by-token LLM delivery
- MCP server: 21 tools, 3 resources, 6 prompts, dual-transport (stdio + SSE)
- Browser-native voice I/O with auto-speak on critical security notifications
Platform Engineering
- JWT + RBAC auth with tenant isolation across 127 endpoints + JSONL audit trails
- 11 OWASP headers, CSP nonces, circuit breaker, token-bucket rate limiting
- CI/CD: Ruff, Bandit, pip-audit, 2,380-test suite, multi-stage Docker builds
Get Help Now
Select the type of request below. Our intake process ensures you get the right tech, right away.
Your Information
// Let us know who we're helping
Device & System Info
// Tell us about the machine
Windows + Pause — or right-click Start → System. Shows CPU, RAM, and Windows version.Ctrl + Shift + Esc → Performance tab → GPU.Windows + R, type msinfo32, press Enter — shows everything at once.🍎 Apple menu in the top-left corner.About This Mac — shows chip, memory, and macOS version.More Info... then scroll to Storage to see drive size.Issue Details
// Describe what's happening
Urgency & Authorization
// Set priority and give us access
Thanks for reaching out to Twilight Tech. We've received your repair request and will contact you within your selected urgency window. Check your email for a confirmation.
Email Us Directly →- CPURyzen 5 5600 or Intel i5-12400
- RAM16 GB DDR4
- Storage500 GB NVMe SSD
- GPUIntegrated / RX 6500 XT
- CPURyzen 7 7700X or Intel i7-13700
- RAM32 GB DDR5
- Storage1 TB NVMe SSD (Gen 4)
- GPURTX 4060 or RX 7600 XT
- CPURyzen 9 7900X or Intel i9-13900K
- RAM64 GB DDR5
- Storage2 TB NVMe + 4 TB HDD
- GPURTX 4080 or RX 7900 XTX
All tiers are starting points — every build is fully customized to your needs and budget. ↓ Fill out the form below.
Your Information
// Who is this build for?
Build Purpose
// What will this machine do?
Budget
// Set your price range
Components & Preferences
// What matters most to you?
Timeline & Delivery
// When do you need it?
Your custom PC build request is in. Twilight Tech will review your specs and budget and send you a custom parts list and quote within 1–2 business days.
Email Us Directly →Let's Talk
Ready to get started, need a one-time service, or just want to understand your security posture? Whether you're a small business owner or a fellow security engineer — Twilight Tech is standing by.